A startling privacy oversight has exposed how senior Trump administration officials inadvertently revealed sensitive connections through Venmo, just days after a confidential Signal group chat about military operations in Yemen was compromised. The mobile payment app, which defaults to public visibility of users’ contacts unless manually adjusted, displayed networks of government officials, journalists, defense contractors, and military personnel—raising alarms among national security experts about potential exploitation by foreign intelligence services.
The controversy began when The Atlantic reported that its editor-in-chief had been mistakenly added to a Signal chat involving top administration officials discussing plans for a March 15 U.S. strike against Iranian-backed Houthi rebels. Soon after, reporters discovered that several officials in the chat had left their Venmo accounts publicly accessible, exposing their professional and personal connections.
Venmo’s Privacy Risks Come Under Scrutiny
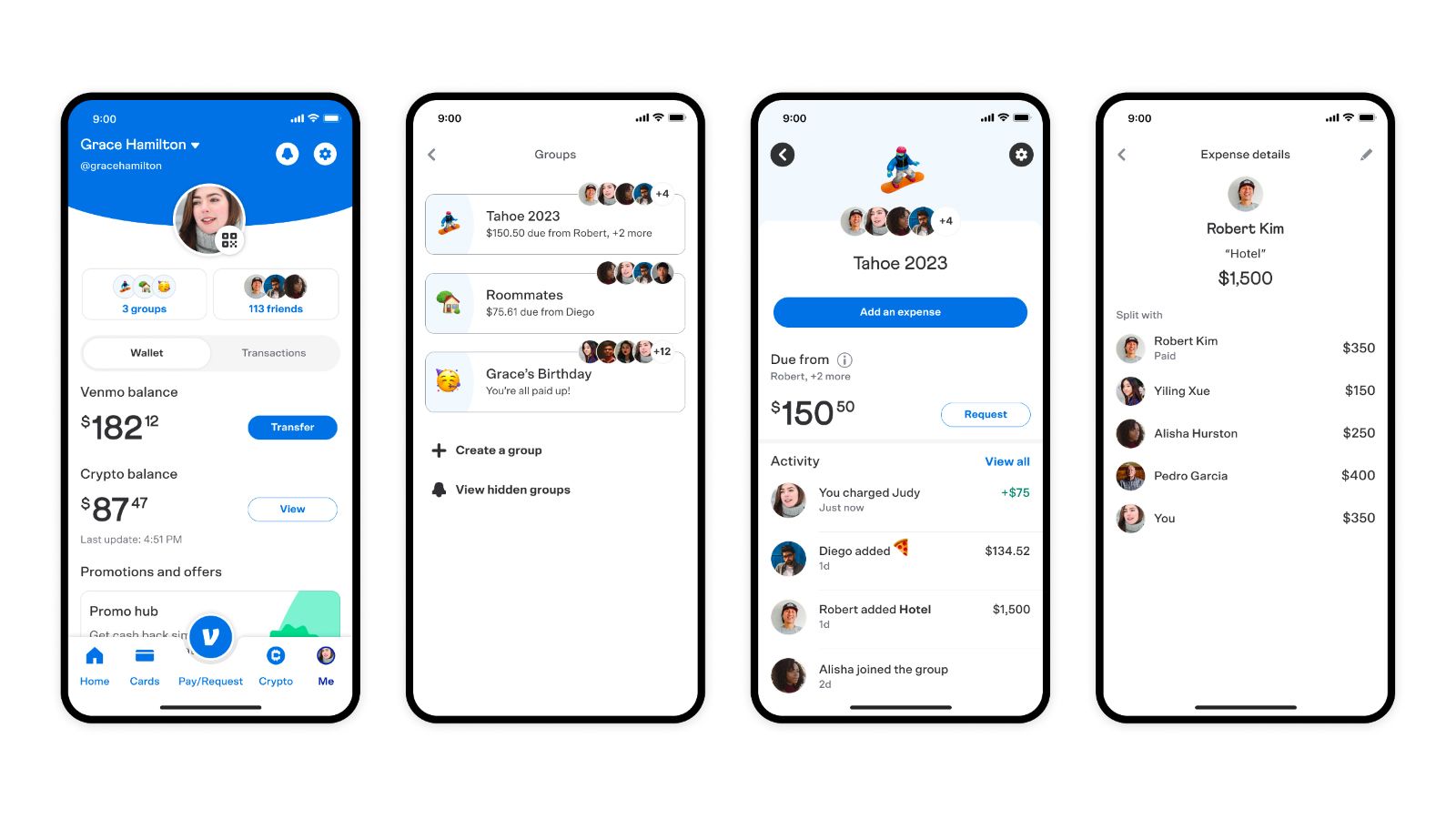
Venmo, a PayPal-owned service designed for peer-to-peer payments, has long been criticized for its lax privacy settings. By default, users’ friend lists and transaction histories are visible to the public—a feature intended for social engagement but one that poses significant risks for government personnel.
- Michael Waltz, White House national security adviser, had his Venmo contacts publicly viewable until Wednesday, a day after The Atlantic’s report. His friends list included Susie Wiles (President Trump’s chief of staff), journalists, active and retired military personnel, and members of Congress.
- Pete Hegseth, Defense Secretary, previously had his Venmo account exposed in February, revealing connections to defense contractors, Fox News colleagues, and UnitedHealth executives. His account has since been deactivated.
- Joe Kent, Trump’s nominee to lead the National Counterterrorism Center, still had a public Venmo profile as of Thursday morning.
After inquiries from CBS News and Wired, Waltz and Wiles locked down their accounts. The National Security Council stated that Waltz had “made necessary updates for his personal privacy protection.
Signal Chat Leak Reveals Operational Details
The initial security lapse occurred when The Atlantic’s editor was added to a Signal group where officials, including Director of National Intelligence Tulsi Gabbard and CIA Director John Ratcliffe, discussed the Yemen strike. While Gabbard and Ratcliffe denied sharing classified intelligence, leaked messages showed Hegseth providing detailed operational updates, including:
- Timelines for fighter jet deployments
- Specifics on weapons used in the strike
- Real-time coordination among officials
U.S. intelligence officials told CBS News that such information is always classified, and even if deemed unclassified, its dissemination violates cybersecurity protocols.
Broader Implications for Digital Security in Government
The incident underscores a growing dilemma: even encrypted apps like Signal, often considered secure, can become liabilities when used improperly. An NSA bulletin obtained by CBS News warned employees a month before the Yemen chat was created that third-party messaging apps should never be used for sensitive discussions, even if unclassified.
Key concerns include:
- Foreign intelligence harvesting: Public Venmo data could help adversaries map out U.S. officials’ networks.
- Operational security breaches: Casual discussions on Signal or Venmo might inadvertently reveal patterns or contacts useful to hostile actors.
- Inconsistent enforcement: Despite policies against using social media for sensitive communications, high-ranking officials continue to do so.
A Pattern of High-Profile Digital Missteps
This is not the first time Trump administration officials have faced scrutiny over digital security:
- In 2023, Der Spiegel reported that personal data—including phone numbers and emails—of several officials had leaked online.
- Previous administrations have also grappled with staff using personal devices for work, but the combination of Venmo, Signal, and classified discussions marks a new level of exposure.
What Happens Next?
The White House has not announced formal disciplinary actions, but the fallout may prompt:
- Stricter social media policies for officials.
- Mandatory privacy training on apps like Venmo.
- Increased scrutiny of encrypted messaging use in government.
For now, the incident serves as a stark reminder: in an era of digital interconnectedness, even mundane apps can become national security vulnerabilities.
If Venmo friend lists can expose government networks, what other seemingly harmless platforms might be hiding similar risks? As officials rush to lock down their accounts, one thing is clear—privacy in the digital age is anything but automatic.
















Add Comment