A Familiar Face with a Malicious Twist
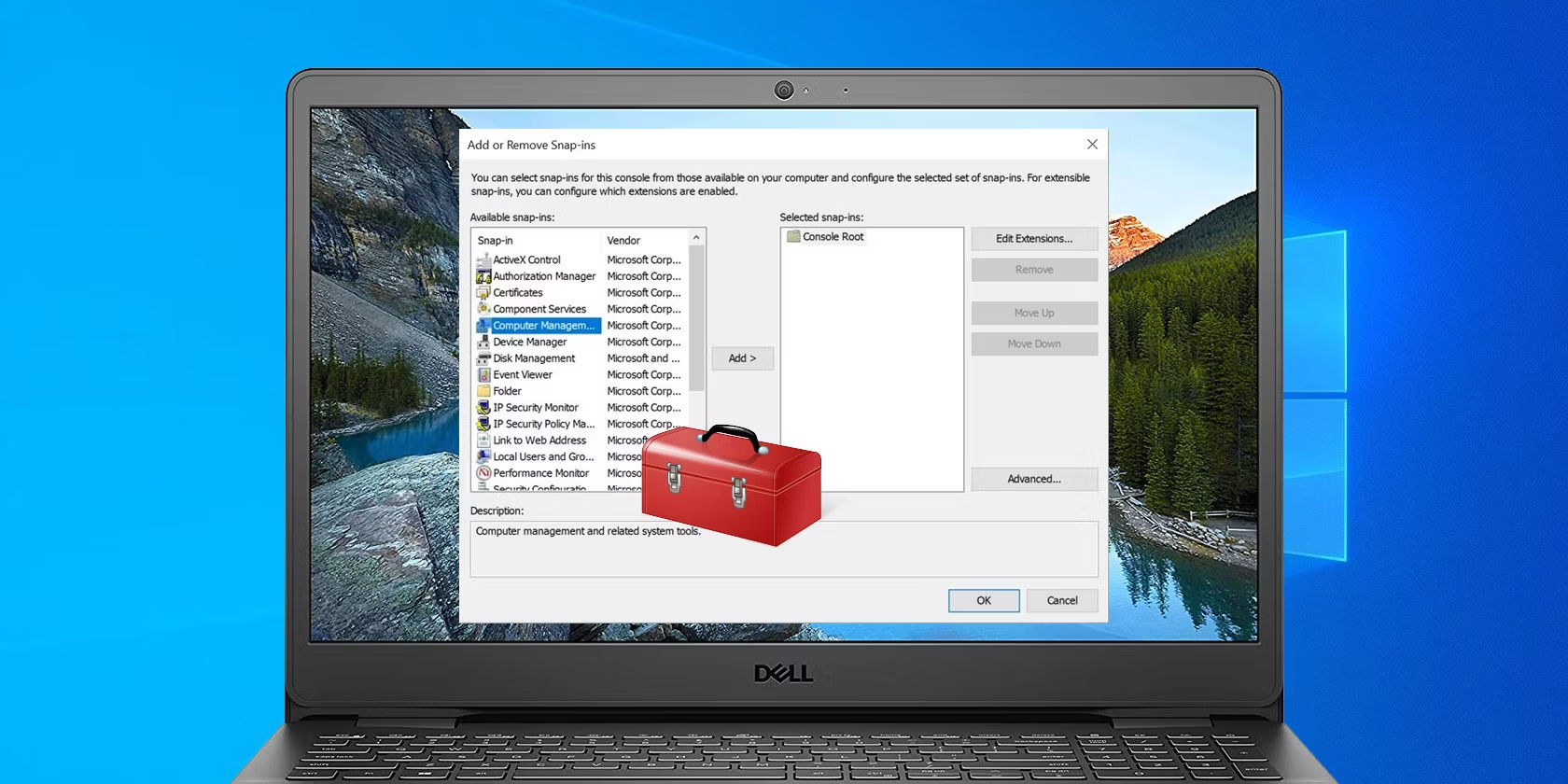
The use of MMC files as an attack vector is particularly concerning because these files are often perceived as benign. System administrators routinely use them to access and manage various Windows settings and tools. This inherent trust allows attackers to disguise malicious code within seemingly legitimate MMC files, potentially bypassing security protocols.
The GrimResource Chain of Infection
- Targeted Delivery: The initial phase involves delivering the malicious MMC file to the target system. This could occur through various methods, such as phishing emails containing infected attachments or compromised websites hosting the malicious files.
- Exploiting a Flaw: Once the victim opens the specially crafted MMC file, the vulnerability in apds.dll comes into play. The malicious code embedded within the file leverages this flaw to execute arbitrary JavaScript code within the context of the mmc.exe process.
- Escalating Privileges: The injected JavaScript code often acts as a springboard for further exploitation. It might download additional malware or utilize techniques like DotNetToJscript to achieve full code execution within the system. This elevated access allows attackers to perform a wider range of malicious activities, such as stealing sensitive data, installing ransomware, or disrupting critical system functions.
- Evasion Tactics: The GrimResource technique incorporates various evasion tactics to make detection more challenging. The use of obfuscation techniques makes it difficult for security software to identify the malicious code within the MMC file. Additionally, the attack leverages legitimate system functionalities like MMC and DotNetToJscript, making it appear like normal system processes.
A Cause for Concern: Why GrimResource Matters
- Exploiting Trust in Commonplace Files: The use of MMC files as an attack vector highlights the ever-evolving tactics employed by cybercriminals. It underscores the importance of being cautious even with seemingly harmless file types.
- Bypassing Security Measures: The ability of GrimResource to bypass traditional security protocols emphasizes the need for layered security approaches. Antivirus software alone might not be sufficient to detect and prevent this type of attack.
- Potential for Widespread Impact: MMC is a widely used tool within Windows environments. A successful GrimResource attack could potentially compromise a vast array of systems, particularly those within corporate networks where MMC plays a crucial role in system administration.
Protecting Yourself from GrimResource Attacks
- Security Awareness Training: Educating users about social engineering tactics and the importance of caution when opening attachments or downloading files, regardless of their perceived source, is crucial.
- Patch Management: Keeping Windows systems and software applications up-to-date with the latest security patches is essential. This ensures known vulnerabilities are addressed and reduces the attack surface for malicious actors.
- Endpoint Detection and Response (EDR) Solutions: Implementing EDR solutions that monitor system activity and can detect suspicious behavior can be invaluable in identifying and mitigating attacks like GrimResource.
- Least Privilege Principle: Following the principle of least privilege grants users only the level of access they need to perform their tasks. This can minimize the potential damage caused by a successful attack.
The Evolving Threat Landscape: Staying Vigilant
The GrimResource exploit serves as a stark reminder of the ever-evolving cyber threat landscape. As attackers develop new techniques, it’s crucial for users and organizations to remain vigilant and implement robust security measures. By staying informed about the latest threats, practicing safe computing habits, and deploying effective security solutions, we can collectively minimize the risk of falling victim to these sophisticated attacks.
The Race for Solutions: Microsoft and Security Researchers Collaborate
With the GrimResource vulnerability in the wild, the focus now shifts to developing a permanent solution. Elastic Security Labs, the team who discovered the exploit, has responsibly reported it to Microsoft. We can expect Microsoft to issue a security patch in the coming weeks that addresses the flaw within the apds.dll library, effectively plugging the hole exploited by the GrimResource attack.















Add Comment